Main navigation
News
- Academic Regulations and Records Office
- (-) Computing Services Centre
- Department of Computer Science
- Department of Electrical Engineering
- Department of Information Systems
- Department of Marketing
- Enterprise Solutions Office
- Facilities Management Office
- Finance Office
- Human Resources Office
- Internal Audit Office
- Office of the President
- Office of the Vice-President (Administration)
- Research Grants and Contracts Office
- Run Run Shaw Library
- School of Law
- Shenzhen Research Institute
- Student Development Services
- Talent and Education Development Office
by by Henry Wong

With all staff mailboxes migrated to Office 365 (O365), the migration of on-premises email supporting tools is underway. One significant upgrade is the migration of on-premises email anti-spam tool to the O365 Exchange Online Protection (EOP) cloud-hosted email filtering service. The migration has ...
by by Joe Chow

Handheld devices such as smart phones and tablets are so popular nowadays that their daily use frequently touch on sensitive and personal data such as email messages, conversational records, contacts, calendar events and even bank transactions. Many people replace their old devices but do not know ...
by by Tony Chan

In view of the increasing popularity of Macintosh (Mac) computers in the University, the Computing Services Centre (CSC) has expanded the support to our Mac users. Following is the list of supported services for Mac computers: · Campus Network (CTNET) Connectivity o Fixed Network Point It allows Mac ...
by JUCC ISTF

/* The following article is extracted from the "Information Security Newsletter" published by the JUCC IS Task Force. */ ? Relationship with ISMS Information Security Management System (ISMS) is defined in the ISO/IEC 27000 set of standards. The ISO/IEC 27001 standard sets out a certifiable and ...
by JUCC ISTF

/* The following article is extracted from the "Information Security Newsletter" published by the JUCC IS Task Force. */ ? The NIST Definition of Cloud Computing 1 The cloud model is composed of 5 essential characteristics (Ondemand self-services; Broad network access; Resource pooling; Rapid ...
by Joe Lee
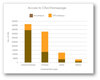
Users have different preferences on using Internet browsers. Preferences may vary from place to place and change over time. We share with you the usage statistics collected in four scenarios. (1) Browser preferences of users accessing the City University Homepage The bar chart below depicts the ...
by ML Lee
In today’s office environment, we often share information like reports, presentations and minutes among colleagues. We have been taught how to connect to the departmental share drive through a network drive letter to store and access files in a traditional file folder structure. This works quite ...
by Maria Chin

Microsoft launched its latest version of operating system (OS), Windows 10, in July 2015. In the article on “Windows 10 at First Glimpse” ( Ref: Network Computing Issue 85 - September 2015), some of the key new features in Windows 10 were highlighted, and the plan to release it first on centrally ...
by Dick Wong

A new upgrade of the campus network had already been started with Phase I (replace/upgrade the network switches at the core and distribution layers) being completed in 2015. The existing network design adopted a traditional 3-tier hierarchical model comprising the core, distribution and access ...
by JUCC ISTF

/* The following article is extracted from the "Information Security Newsletter" published by the JUCC IS Task Force. */ The term APT was first used by U.S. Air Force back in 2006 to facilitate discussion about a set intrusion activities with specific characteristics. These days, APT is often used ...